SUMMARY The application of AI and machine learning to enterprise network operations is not a new concept. AIOps has made great strides over the past several years to improve resiliency through deeper assurance and by providing higher levels of security. However, the complexity of today’s networks — resulting from continued disaggregation and cloudification — is taxing the application of traditional AIOps tools. Ethernet’s continued evolution and modern network scale-up, -out, and -across architectures hold great promise in addressing these challenges, as do emerging agentic AI frameworks to facilitate deeper automation. Despite these advancements, more is needed to support the performance and automation requirements of campus, branch, and datacenter network deployments…
-
-
SUMMARY Modern AI, including generative and agentic applications, has great promise. It can transform centralized and edge datacenter operations, supercharge workloads, and streamline use cases. Furthermore, mobile networks stand to benefit from next-generation AIOps thanks to enhanced agility in communication service provider provisioning and management, as well as higher availability — all realized through automation. Future mobile network standards, including 5G Advanced and 6G, are expected to not only incorporate AI into the radio access network layer, but also the core and transport functions. This should help optimize performance, ease management, reduce energy expenses, and more. However, there are multiple barriers to entry within the modern AIOps journey, including the…
-
SUMMARY The rising adoption of generative AI tools and agentic frameworks present a multitude of challenges to enterprise networking operations teams that are struggling to ensure robust connectivity and security at scale. Simultaneously, multi-cloud and on-premises infrastructure deployments, and emerging edge and hybrid AI use cases, are creating operational friction in the form of poor visibility and assurance. This is resulting in more frequent enterprise connectivity outages, longer mean time to resolution of faults and recovery, and unwanted business disruption. Enterprises view the use of modern AI as a competitive advantage. Universal DDI services that include domain name system (DNS), dynamic host configuration protocol (DHCP), and IP address management (IPAM)…
-
SUMMARY Broad industry efforts — including Secure by Design, the National Institute of Standards and Technology (NIST) Cybersecurity Framework, the Joint Cyber Defense Collaborative within CISA, and widespread threat intelligence sharing — have bolstered cybersecurity defenses. Still, bad actors continue finding new ways to compromise security controls across infrastructure solution providers. It represents an unprecedented onslaught, further intensified by the rise of nation-state attacks buoyed by an ongoing and unstable geopolitical climate. Modern generative and agentic AI tools have great promise for fortifying security posture and defense within cybersecurity platforms. However, cyber criminals are also leveraging the same technologies to improve the sophistication of attacks to disrupt operational efficiency and…
-
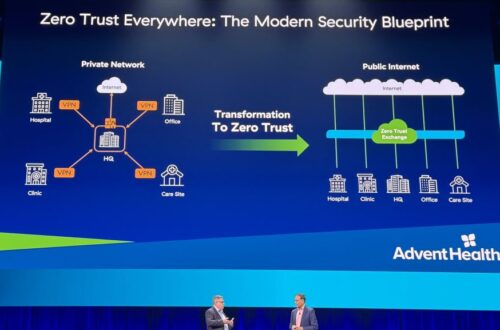
SUMMARY Traditional reactive detect and respond methodologies to address cybersecurity needs are quickly becoming ineffective. Bad actors in growing numbers are weaponizing generative AI applications to dramatically improve the sophistication of cyberattacks for illicit ransomware gains. Furthermore, the use of emerging agentic AI frameworks by criminals to scale the speed and volume of threats is also troubling. Modern AI tools are fortifying cyber defense, but they represent a double-edged sword — also unlocking the ability for attackers to develop unique, single-use malware that renders reactive security solutions obsolete. To address these challenges, a preemptive cybersecurity architecture to harden security is required. A design approach rooted in the Domain Name System…
-
SUMMARY Networking has evolved dramatically over the past five decades. The birth of the first network in the late 1960s brought with it the power to connect computational devices intended to improve productivity and collaboration. The creation of Ethernet in the 1970s streamlined networking, as did other efforts to standardize connectivity on a wide scale for personal computers and servers in the 1980s. Public access to the internet in the 1990s redefined the ability to connect people, places, and things, as did cellular mobile networks in the 2000s, delivering higher levels of untethered access and data capacity with the advent of the 3G standard. Within the past decade, machine learning…
-
SUMMARY Enterprise IT professionals face daunting challenges in the highly disaggregated environment of today’s IT infrastructures. The desire to manage this complexity often leads to the prescriptive use of tech stacks and programming tools pinned to specific public-cloud and on-premises deployments. Unfortunately, developer efficiency and innovation can be stifled due to this approach. Furthermore, the need to ensure the highest levels of secure code can often lead to less time spent empowering developers to deliver innovative applications and services. When it comes to supporting developer operations, organizations must strike a balance that enables both innovation and security. Simply embracing CI/CD pipelines is not enough, as seen in recent operational stumbles…
-
SUMMARY Astonishingly, only half of the world’s population is connected to the internet. It is a complex problem, exacerbated by regions of smaller population densities and the capital and operational expense outlays tied to deploying expansive public fiber and traditional public mobile networks. Private 4G LTE and 5G cellular networks and fixed wireless access deployments have great promise in both industrial use case transformation and closing the global digital divide. These solutions offer connectivity diversity, leveraging the provisioning flexibility and cost-effective coverage required for less densely populated regions — ultimately providing fiber-like performance powered by the lower latency and performance profiles enabled by 5G. Coverage gaps will continue to persist,…
-
SUMMARY Cloud computing continues to deliver transformative capabilities for organizations of all sizes. Its ability to scale resources based on demand, improve accessibility, reduce infrastructure costs, and enable quick deployment of applications is without question. However, the continued growth and adoption of cloud-native applications, as well as multi-cloud and hybrid cloud infrastructure deployments, present challenges for enterprises. For starters, developers are often forced to spend less time creating value-added features in lieu of prescriptive coding to ensure the highest levels of security. Furthermore, cloud tool sprawl in the absence of fully integrated solutions tends to reduce productivity, delay time-to-market and slow innovation. This all leads to the adoption of manual…
-
SUMMARY Communications service providers (CSPs) face daunting economic and operational challenges. On one hand, capital expense levels and management complexity tied to next-generation mobile core, radio access network, and backhaul deployment continue to be significant despite the introduction of disaggregated infrastructure and Open RAN systems. The sky-high cost of licensed spectrum used for data transmission and service support also adds to this burden. On the other hand, operator monetization beyond access remains an elusive endeavor because of legacy constraints, persistent security challenges, and friction tied to a historical lack of developer tools to facilitate fixed, mobile, and converged network programmability. AI and automation combined have great potential to help CSPs…
-
Protecting the Datacenter, Client, and Network Edge Next-generation enterprise AI is poised to become one of the most disruptive technology platforms introduced in decades, if not this century. It has the potential to unlock newfound efficiencies within enterprise IT and OT operations and incubate new business value. However, as with any leapfrog infrastructure advancement, bad actors will attempt to exploit vulnerabilities for financial gain and other advantages. Thus, organizations must defend against AI weaponization across the entire network expanse—from datacenters on-premises or in the cloud, to clients at the network edge. Enterprise AI LLMs and the underlying algorithms represent a significant investment and are only valuable if they can be…
-
The rise of artificial intelligence (AI), fueled by the overwhelming popularity of AI- powered language models like ChatGPT, along with the broader generative AI applications, spotlights the importance of data security. The large amount of data AI requires to train models makes data security paramount. Beyond securing the data used to build large language models (LLMs) — public and foundational — protecting the AI models themselves becomes equally important. This is true cross-domain, public and private, on-premises, in the cloud, and at the network edge. You can download the paper below: Source: https://moorinsightsstrategy.com/research-papers/research-paper-intel-protecting-data-and-models-within-emerging-ai-workflows/ Authors: Will Townsend, Patrick Morehead