-
-
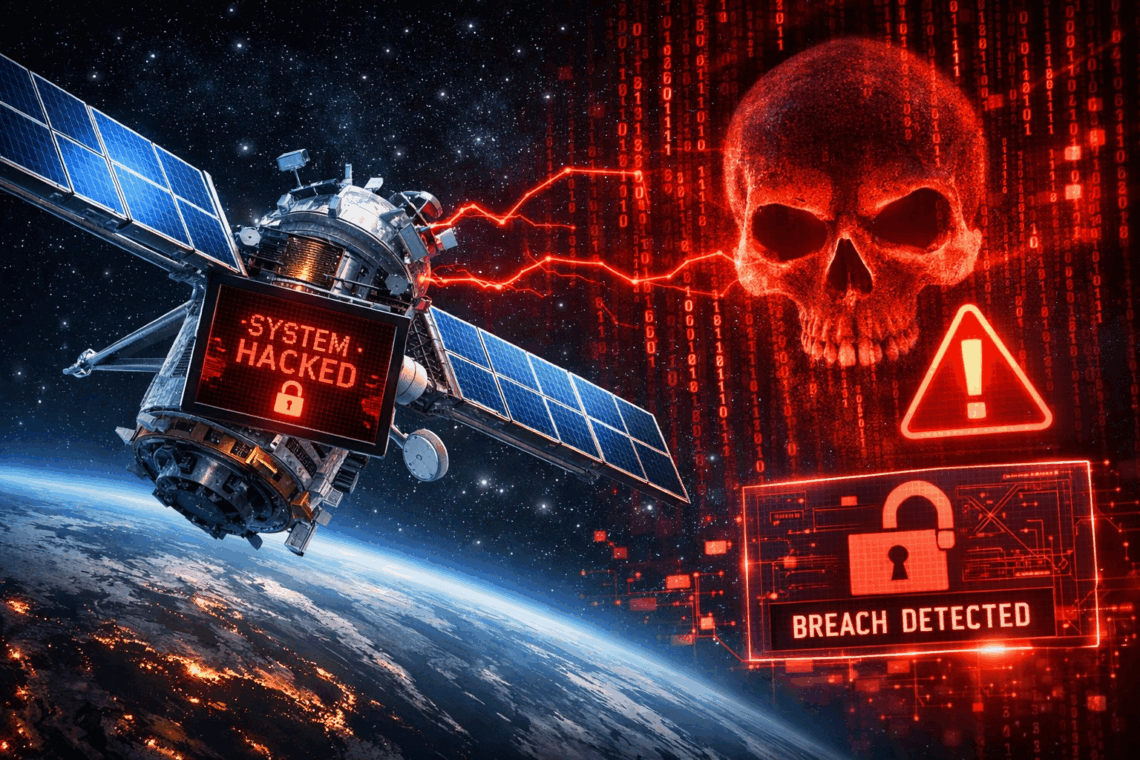
Last year, a group of researchers at UC San Diego and the University of Maryland revealed a startling discovery utilizing an inexpensive satellite receiver system made with off-the-shelf components – not purpose-built spyware. Following three years of data collection and analysis from a vantage point in La Jolla, the team was able to collect a myriad of confidential data from geosynchronous satellites. As mobile network operators, including AT&T, T-Mobile, Vodafone, and others, adopt non-terrestrial networks to expand coverage, the study highlights the need for stronger security provisions. In this research note, I will outline the types of confidential data intercepted, the initial responses from operators, and what should be considered…
-
Gigamon held its fifth annual Visualyze Bootcamp virtual event over three days in early September. Since its founding 20 years ago, the company has developed a deep observability pipeline that leverages network intelligence to detect threats often missed by traditional security tools. The Bootcamp serves as an opportunity for Gigamon to share its industry and technical knowledge with customers. Most organizations using cloud services employ a multi-cloud model to benefit from competitive pricing and access to best-of-breed service offerings. Additionally, the trend toward containerization and virtualization aims to enhance operational and cost efficiencies. However, hybrid cloud deployments can introduce complexities that require careful management. The Bootcamp addressed many of these challenges, with…